See also:
– Anti-Iran computer bug had powerful backers
– Has the West declared cyber war on Iran?
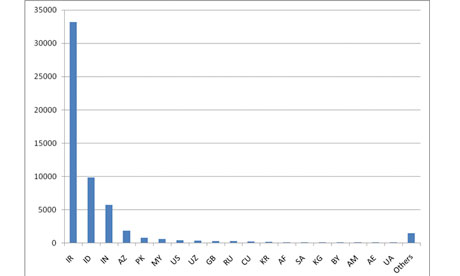
An antivirus expert said the virus has infected over 6 million computer accounts

The Stuxnet computer worm has wreaked havoc in China, infecting millions of computers around the country, state media have reported.
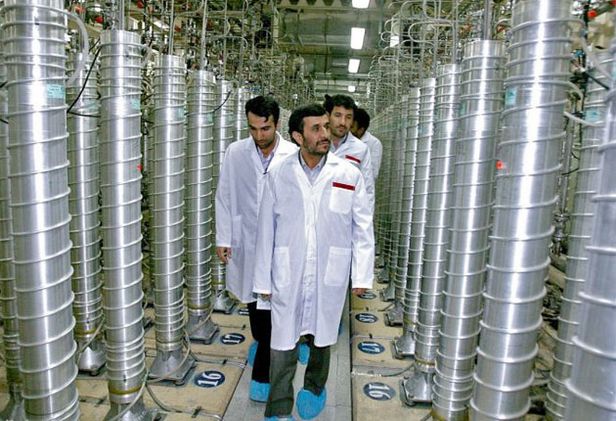
A computer virus dubbed the world’s “first cyber superweapon” by experts and which may have been designed to attack Iran’s nuclear facilities has found a new target — China.
The Stuxnet computer worm has wreaked havoc in China, infecting millions of computers around the country, state media reported this week.
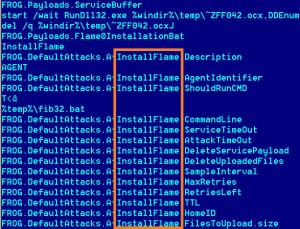
Stuxnet is feared by experts around the globe as it can break into computers that control machinery at the heart of industry, allowing an attacker to assume control of critical systems like pumps, motors, alarms and valves.
It could, technically, make factory boilers explode, destroy gas pipelines or even cause a nuclear plant to malfunction.
The virus targets control systems made by German industrial giant Siemens commonly used to manage water supplies, oil rigs, power plants and other industrial facilities.
“This malware is specially designed to sabotage plants and damage industrial systems, instead of stealing personal data,” an engineer surnamed Wang at antivirus service provider Rising International Software told the Global Times.
“Once Stuxnet successfully penetrates factory computers in China, those industries may collapse, which would damage China’s national security,” he added.
Another unnamed expert at Rising International said the attacks had so far infected more than six million individual accounts and nearly 1,000 corporate accounts around the country, the official Xinhua news agency reported.
Read moreStuxnet ‘Cyber Superweapon’ Wreaks Havoc in China, Infects Millions of Computers